Cyber Security Protects Sensitive Network Data
Safeguard your digital infrastructure with advanced solutions that prevent breaches, ensure compliance, and secure your business’s.
View Case Studie Details
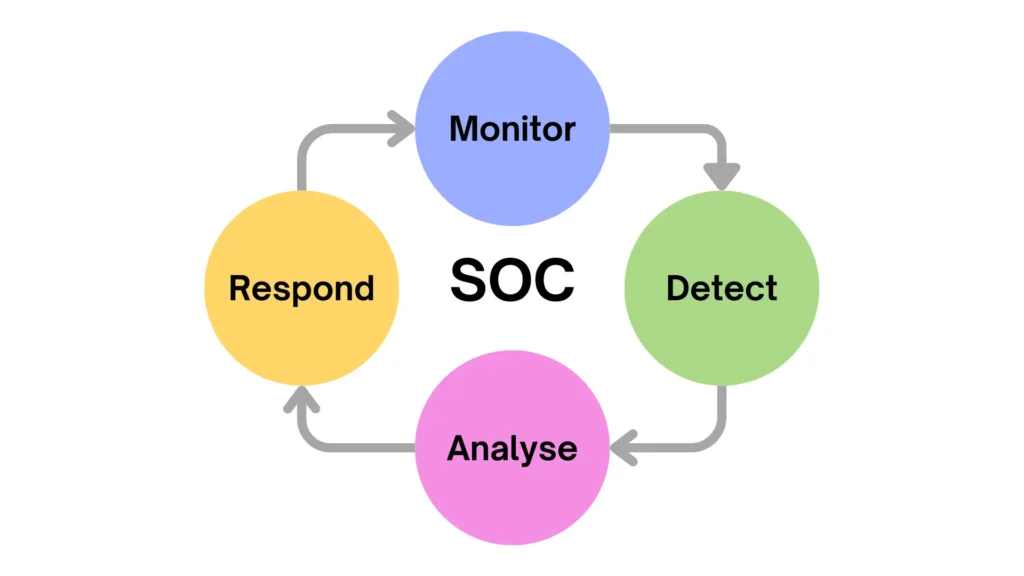
Our Security Operations Center as a Service (SOCaaS)
offering is the response to the modern threats that large,
medium and small enterprises experience today:
• Online security monitoring 8/5 and 24/7
• Managed Detection and Response
• Design, implementation and support of SOCs
• Training and outstaffing Tier I, II, and III SOC personnel
Our SOC experts use the latest technology to monitor your systems 24/7, ensuring rapid threat detection and full regulatory compliance—keeping your business secure and worry-free.


Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
Our Managed Security Services provide end-to-end protection for your applications, ensuring resilience against emerging cyber threats. From proactive threat detection to incident response, we help safeguard your business-critical applications with comprehensive security strategies.
Simulate attacks, discover weaknesses, and fix them fast.
Ready-made and customizable policies to secure your operations.
Managed Security Services provide scalable, expert-driven protection for your applications, cloud, and infrastructure—ensuring continuous defense against evolving cyber threats.
Simulate attacks, discover weaknesses, and fix them fast.
Ready-made and customizable policies to secure your operations.


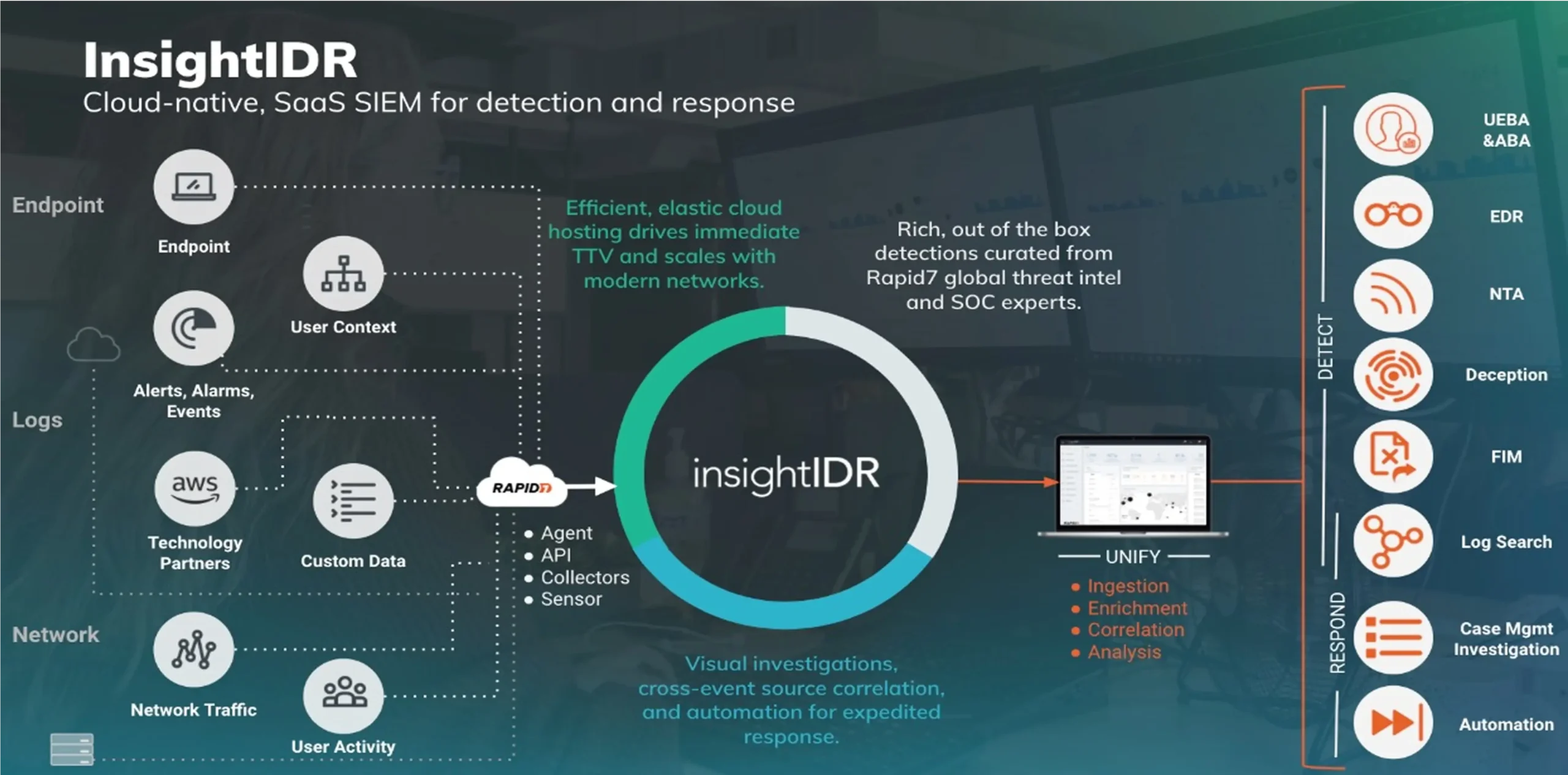
Rapid7 InsightIDR is a cloud-based Security Information and Event Management (SIEM) solution designed to help organizations detect, investigate, and respond to cyber threats quickly. It provides real-time threat detection, user behavior analytics, and endpoint monitoring to identify suspicious activity across networks, applications, and cloud environments. InsightIDR also offers automated incident response, centralized log management, and compliance reporting, enabling security teams to reduce dwell time, improve visibility, and strengthen their overall security posture.

We provide end-to-end SOC design, implementation, and outsourcing, supporting clients across the Netherlands, Germany, Texas, Portugal, the Philippines, Israel, the UK, and more. Our IT outsourcing services include outstaffing skilled cybersecurity and IT personnel at junior, middle, and senior levels, all with professional certifications. Flexible engagement options are available—full- or part-time, fixed price or hourly—with very attractive rates and B2-C1 English proficiency.


Have questions about cybersecurity or how our services protect your business? Explore quick answers to the most common concerns about threats, data protection, and compliance.
Information security refers to the practices and tools used to protect sensitive data from unauthorized access, misuse, or destruction. It ensures confidentiality, integrity, and availability of information.
Keep your operating system and software updated, install antivirus software, use strong passwords, enable a firewall, and avoid clicking unknown links or downloading suspicious files.
Data management involves collecting, storing, organizing, and protecting data throughout its lifecycle. It ensures data is accurate, accessible, and secure while complying with privacy regulations.
You’re responsible for safeguarding data you access, reporting suspicious activity, following security policies, and using tools responsibly to prevent data leaks or cyber threats.
Only if the email is encrypted and follows your organization’s data protection policies. Unencrypted email is not secure and should not be used to transmit sensitive or confidential information.

Infosec Manager, FinTech Company

CTO, Cybersecurity Company

CEO, Cybersecurity Company

VP Of Operations, MedNova Health Solutions
"Communications were clear, efficient, and professional. Apex Digital Systems provided actionable solutions and kept us informed every step of the way."

"The Apex team was easy to work with, highly responsive, and provided practical cybersecurity recommendations that improved our overall security posture."

"Apex Digital Systems significantly enhanced the security of our cloud and web infrastructure."

"Working with Apex Digital Systems was seamless; they delivered exactly what we needed."

"Everything went smoothly; the team is highly professional and knowledgeable."

"What impressed us most was Apex Digital Systems’ customer-first approach and flexibility in meeting our unique needs."

"We were impressed by their proactive approach and dedication to securing our systems effectively."

"The project management by Apex Digital Systems was flawless, ensuring timely delivery and high-quality outcomes."

Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam.
Safeguard your digital infrastructure with advanced solutions that prevent breaches, ensure compliance, and secure your business’s.
View Case Studie DetailsEmpower your team with the knowledge and habits needed to detect, prevent, and respond to security.
View Case Studie DetailsSafeguard your digital infrastructure with advanced solutions that prevent breaches, ensure compliance, and secure your business’s.
View Case Studie DetailsManaged Security Services provide scalable, expert-driven protection for your applications, cloud, and infrastructure—ensuring continuous defense against evolving cyber threats.
Simulate attacks, discover weaknesses, and fix them fast.
Ready-made and customizable policies to secure your operations.